Sometime it’s the fundamentals that get missed when you are in FireDrill mode for too long and need to get things done. Or maybe you inherited a fileserver where there are WAY too many admins and you are troubleshooting access issues. Take a moment, step back and revisit the basics of Group strategies and how they should be applied to all sorts of scenarios. You have to understand the history before you can start with the new stuff.
Wait a second. You’re talking about everyday boring groups? Those things you use to group users together so that you can assign access rights to resources? How is this going to help me regain control of users? Let me share a story.
 Recently I inherited a Clustered FileServer that had a couple of thousand users who accessed resources from many, many domains across this international Active Directory forest. Upon further examination, the use of groups WAS employed (poorly), but only ONE GROUP was created. This group gave whoever was a member “Full Control” of the file permissions down through the entire folder structure on the server. On top of that – it was used across a dozen different shares, accessed by different groups of users across the entire organization. This fileserver was running on aging hardware, constantly getting “full” and was due for a swap to a new solution. How do I handle this while continuing to work on my regular day job?
Recently I inherited a Clustered FileServer that had a couple of thousand users who accessed resources from many, many domains across this international Active Directory forest. Upon further examination, the use of groups WAS employed (poorly), but only ONE GROUP was created. This group gave whoever was a member “Full Control” of the file permissions down through the entire folder structure on the server. On top of that – it was used across a dozen different shares, accessed by different groups of users across the entire organization. This fileserver was running on aging hardware, constantly getting “full” and was due for a swap to a new solution. How do I handle this while continuing to work on my regular day job?
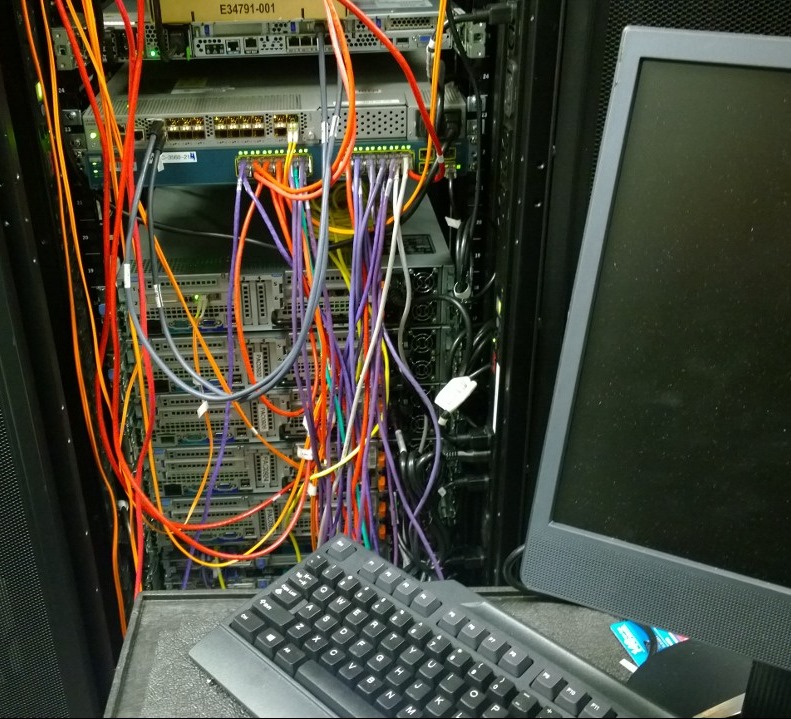
Procuring the new hardware was easy.
I ordered up a nice 70 terabyte Cluster-In-A-Box from DataOnStorage and got it setup as a Clustered Fileserver. After establishing a large DrivePool and carving out a new Dual Parity StorageSpace – I set about doing some basic Group planning for future access.
Every SysAdmin has their own philosophy on how to assign access rights to shares and folder permissions. There have been some enhancements with Windows Server 2012 R2, but fundamentally things have not changed all that much (A,G,DL,P):
Assign users into
Global Groups. Nest them inside
Domain Local groups and Assign
Permissions to the share / folder structure.
Why do I bring this up? You would be surprised at the number of times I’ve see ACLs (Access Control Lists) for folders / shares that have individual users added directly added to them. Usually as a result of someone granting Full Control to a non technical person (who has no background in managing servers) and them getting a little too advanced for themselves by changing file permissions, only to “Apply this to all files and sub folders”.
Do yourself a favor. Please explain this concept to anyone who will be managing a folder structure or share on a server. DON’T MAKE THE ASSUMPTION that they know what you are talking about. But also explain to them about reusing groups where it makes sense and possibly “mail enabling” groups in order to make them multi-purposed. A well managed AD with an understood and communicated Group Strategy will go a LONG way to keep your sanity, keep the users in line and reign in wayward file servers.
That migration project for the file server? It’s almost done. I’ve practiced what I’ve preached here and contacted the respective owners of the various shares to re-confirm what their requested level of security is. I’ve create groups and nested them inside local groups on the new server. I’ve also “trained” the owner of the shares what groups are being used and I’ve delegated them the rights to go an manage the group memberships to ultimately control who has access to the resources. I’ve setup some RoboCopy command scripts to copy over data and synchronize data. I’m almost ready to flip the switch – just got to get back from my travels on the road and send out the notification emails.
I think some of the follow up from the final process would make a good couple of posts. Stay tuned for more.
If you can’t wait and need to make sometime to figure out what’s coming around the bend – check out the new EvalCenter with it’s concept of “Tech Journeys” and explore some Hybrid datacenter concepts or Mobile Device Management. .